Product Update: Automate alerts to your social media
Escape has created the first ever push-to-post automation to revolutionize vulnerability management by giving you the recognition you deserve.
Discovering vulnerabilities is half of the game, but what the industry is still yet to address is getting your due recognition when you do discover them.
That's why at Escape we are thrilled to announce the first ever push-to-post workflow automation, where as soon as your vulnerabilities are discovered, they can be posted straight to your social media platforms for everyone to see your hard work.
Being a security engineer is always about being behind the scenes. You run the scans, you validate the results, but you never get the credit you deserve for uncovering critical vulnerabilities. We're here to change that.
Turn your DevSecOps into DevBragOps with our new feature now.
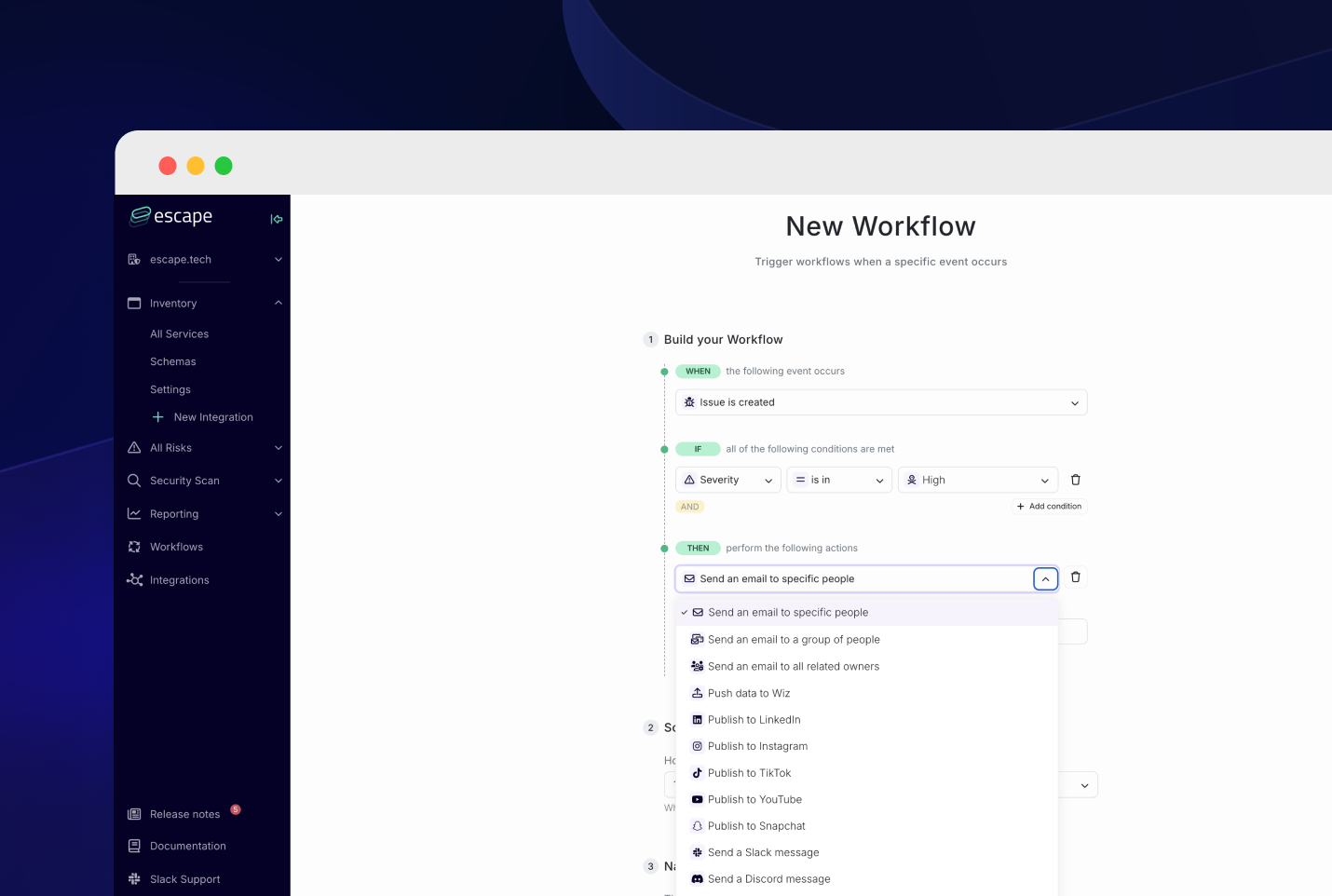
How does it work?
We now have a fully integrated automation pipeline that connects your internal security tooling with external social channels. In the setup, you can choose your preferred social media for posts to go to. Whether that's LinkedIn, so your network knows what's wrong with your internal networks, or TikTok to get some vulnerability virality, we have you covered (or, well, exposed).
How does it work?
- The Escape DAST uncovers a vulnerability.
- Then the workflow automation auto-generates a caption optimized to your preferred platform.
- The caption and a screenshot of the vulnerability findings are automatically posted, with zero manual intervention required.
- If your chosen social media is TikTok or YouTube, we have leveraged AI to create a video of the vulnerability in action and demonstrate any potential attacks, to make it clear how much you've saved the day by discovering it.
Publishing in real-time, there's no more sitting on bugs for 90 days or the endless back-and-forth with legal on what you can say. In our boldest move yet, we want to enable a fully automated discovery-to-disclosure pipeline and make sure everyone possible knows you found a bug.
Key features
Our latest automation not only eliminates the manual burden of disclosure but also leverages AI to ensure maximum engagement:
Timed release: With the Leak Later Lever, you can choose to schedule your posts at peak bragging hours to maximize your network seeing your work.
Shareholder tagging: The tool also makes sure to tag all affected vendors with both their company and the Head of Security's accounts, as well as tagging your manager and any relevant compliance authorities, ensuring everybody involved knows about your discovery.
Optimized captions and hashtags: Our AI bot summarizes your findings with attention-grabbing phrases like "We could lose millions if we don't fix this asap. Here's why:", as well as including top hashtags like #devOops, #ZeroDay, and #AuthBypassed.
Seamless integration into your content schedules: If you're already a securityfluencer, you can integrate your content calendar so that vulnerability posts slot right in for maximum virality opportunity.
Key benefits
- Flex-first, fix second: You can't flex finding a vulnerability if it's already been fixed, so our latest workflow enables you to flex first for optimal bragging timelines.
- Eliminate the manual burden of disclosure content: With automated post generation, you can achieve unfiltered exposure without having to create a single thing, bypassing any pesky content approval frameworks.
- Turn vulnerabilities into viralities: Seamlessly integrate vulnerability discovery into your Clout Integration and Continuous Disclosure pipeline, maximizing the ability to turn a security incident into a career-defining viral moment.
- Increase personal brand visibility: By consistently sharing your findings across social channels, you build credibility by gaining recognition for your work, attract new opportunities, and contribute to wider security dialogues in the community, all with zero extra work in your day.
Our latest automation integrates with your existing CI/CD, vuln scanners, and bug tracking systems. With one toggle, you can turn every finding into a post-ready moment of glory.
We want to revolutionize vulnerability lifecycle management, because in 2025, it’s not just about fixing vulnerabilities - it’s about being seen fixing them.
And if you're concerned about privacy or a hacker exploiting the vulnerability before you can remediate it, then rest assured, this article would not come out on any other day except today : )
Discover more serious product updates (not that this article isn't totally real)
