Burp Suite Alternatives: The Complete 2026 Comparison between Escape and Burp Suite
Escape is the leading Burp Suite alternative for modern application security teams. Unlike Burp Suite, Escape automates business logic testing (IDORs, SSRFs, access control flaws), ensures faster scanning with fewer false positives, and provides remediation code snippets.
Burp Suite is the standard for manual penetration testing and most teams we talk to aren't trying to replace that workflow. The question they're actually asking is different: "Burp does great work when a human is at the keyboard. What do we use the other 51 weeks of the year, when development is shipping faster than a pentester can keep up?"
This article is for security engineers asking that question. We'll walk through where Burp Suite still wins, where its architecture starts to crack under modern AppSec workloads (APIs, SPAs, complex auth, AI-built code), and how Escape's platform fits alongside it or replaces the parts that no longer pull their weight.
TL;DR: How Escape DAST compares to Burp Suite DAST (former Burp Suite Enterprise)
Escape and Burp Suite DAST cater to different needs, whether you're pentesting a single application, scaling across large teams, or automating security testing in CI/CD.
We've built this comparison based on the following sources:
- Official websites
- Demos on YouTube and official documentation
- Feedback from security professionals (whether Burp Suite's and Escape's current customers or not)
| Dimension | Burp Suite | Escape |
|---|---|---|
| Core approach | Manual-first intercepting proxy and active scanner, extended with a plugin ecosystem and a Burp AI assistant for pentesters< | Combination of graph-based knowledge (built within business-logic-aware DAST) + AI-powered multi-step reasoning & specialized offensive agents within AI pentesting product |
| Best at | Highly customizable manual control for fine-tuning scans and handling complex scenarios | Continuous testing across APIs, SPAs, and complex auth, with developer-ready fixes |
| Scope today | Web applications first; APIs supported via manual upload of OpenAPI / Postman / SOAP definitions; GraphQL relies on introspection | APIs (REST, GraphQL), web apps, hosts, ports — already in production |
| Continuous testing | Scheduled scans and CI/CD integration via REST API, but workflows still center on point-in-time scans rather than continuous coverage/td> | Yes — DAST for single step vulnerabilities + triggered AI pentesting |
| Regression testing | Not supported | Supported via AI pentesting. Results within less than 1h from bug bounty and manual pentesting reports |
| Developer handoff | Light remediation | Stack-specific code fixes (Node.js, GraphQL, etc.), tied to asset owners |
| False positive triage | Manual | AI false-positive agent (automated) |
| Compliance support | Reporting only | Ability to build custom reports, compliance matrix for overall posture analysis |
| Automations & workflows | REST API, Jenkins / GitHub Actions / GitLab CI / Azure DevOps via Docker, BApp Store extensions (Java/Python), BChecks for custom rules | Public API, Escape CLI,, custom workflows, multiple integrations, including Claude Code and platforms like Wiz |
| Attack Surface Management | Not a focus | Built-in: assets discovered across code repos and cloud, weighted by business criticality |
| Pricing | Custom enterprise quote based on scan hours and estate size; Pro seats priced separately (~$475/year/user). Two-tier model (Pro + DAST) means most teams pay twice | Platform pricing aligned to scope (number of scans and applications/APIs to test) |
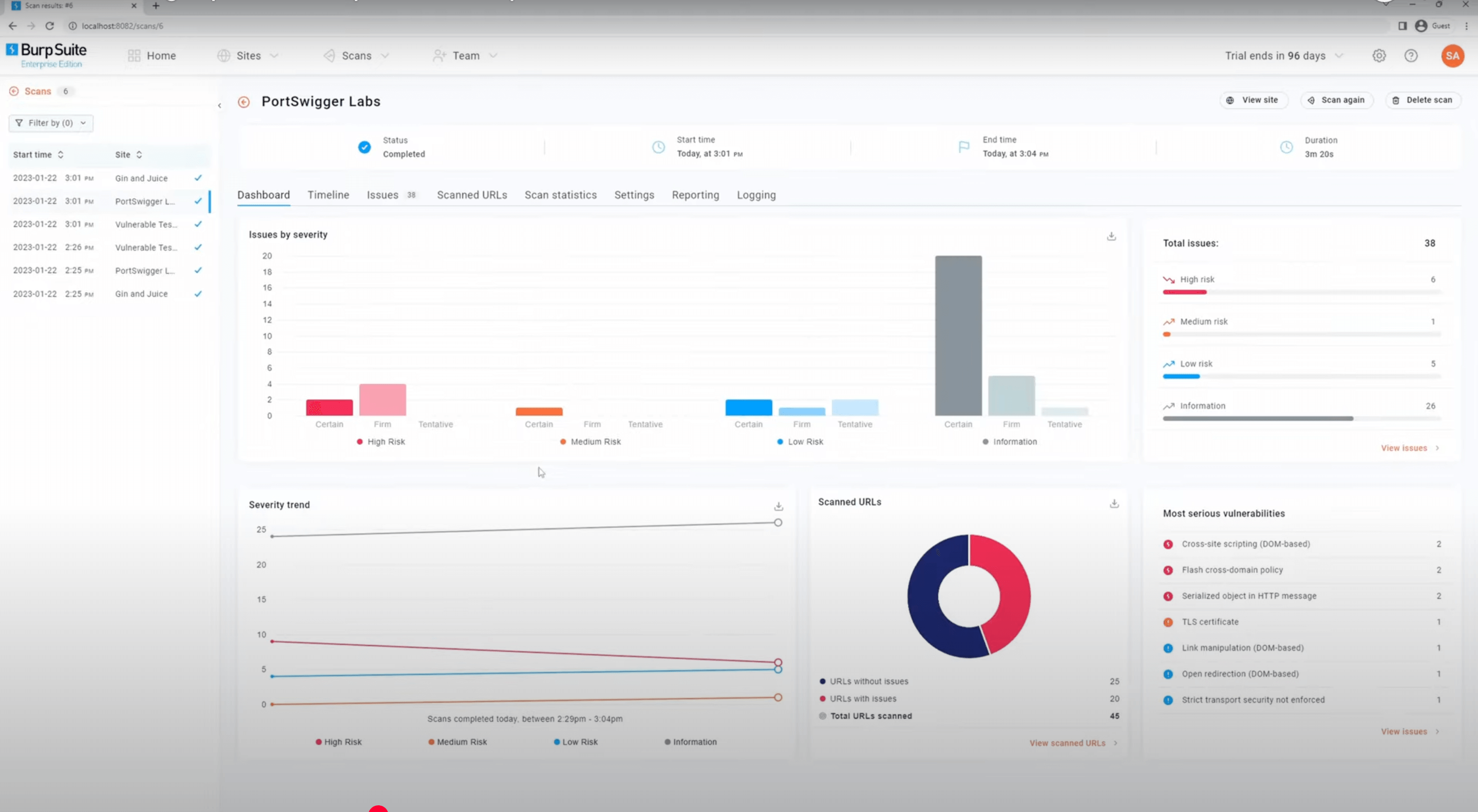
Burp Suite DAST
Pros
✅ Highly customizable with manual control for fine-tuning scans and handling complex scenarios
✅ Extensive support for a wide range of authentication methods
✅ Backed by Burp Suite's ecosystem and community
✅ Supports a large variety of plugins, both free and paid, allowing you to extend its capabilities beyond the out-of-the-box features
Cons
❌ Steep learning curve for beginners due to its complex interface and manual configuration
❌ Resource-intensive; may not perform well on low-end systems during large scans.
❌ Encounters challenges in handling SPAs, especially those involving client-side routing and conditional rendering
❌ Does not fully automate the detection of business logic vulnerabilities
❌ Lack of code owner identification
❌ Offers detailed remediation guidance but no code-level fix suggestions
Escape
Pros
✅ Easy setup: Complex authentication handling & automated API documentation generation that helps you to launch scans right away and reduces the need for maintenance of scans
✅ Custom security tests that do not require maintenance
✅ Business logic testing: finds IDORs, SSRFs and Access control issues in modern web applications
✅ Actionable remediation code snippets for developers tailored to their frameworks
✅ Integrations with advanced tools like Wiz
✅ In-depth application discovery, including internal API discovery from code
Cons
❌ Escape's plugin or extension ecosystem is not as extensive as Burp Suite’s, potentially limiting its extensibility and integration with some of the third-party applications.
❌ Advanced feature sets require specialized knowledge
In-depth feature comparison between Burp Suite DAST and Escape DAST
Complexity of scan setup
Burp Suite DAST
For web applications, Burp Suite offers automated scanning that can crawl and identify vulnerabilities, but for API scans, it requires more manual setup (see Burp Suite docs). Users must upload API definitions such as OpenAPI, Swagger, Postman Collections, or SOAP WSDL, either via URL or file upload. Once the schema is uploaded, Burp validates it and identifies API endpoints for scanning, but users must manually configure all the scan settings.
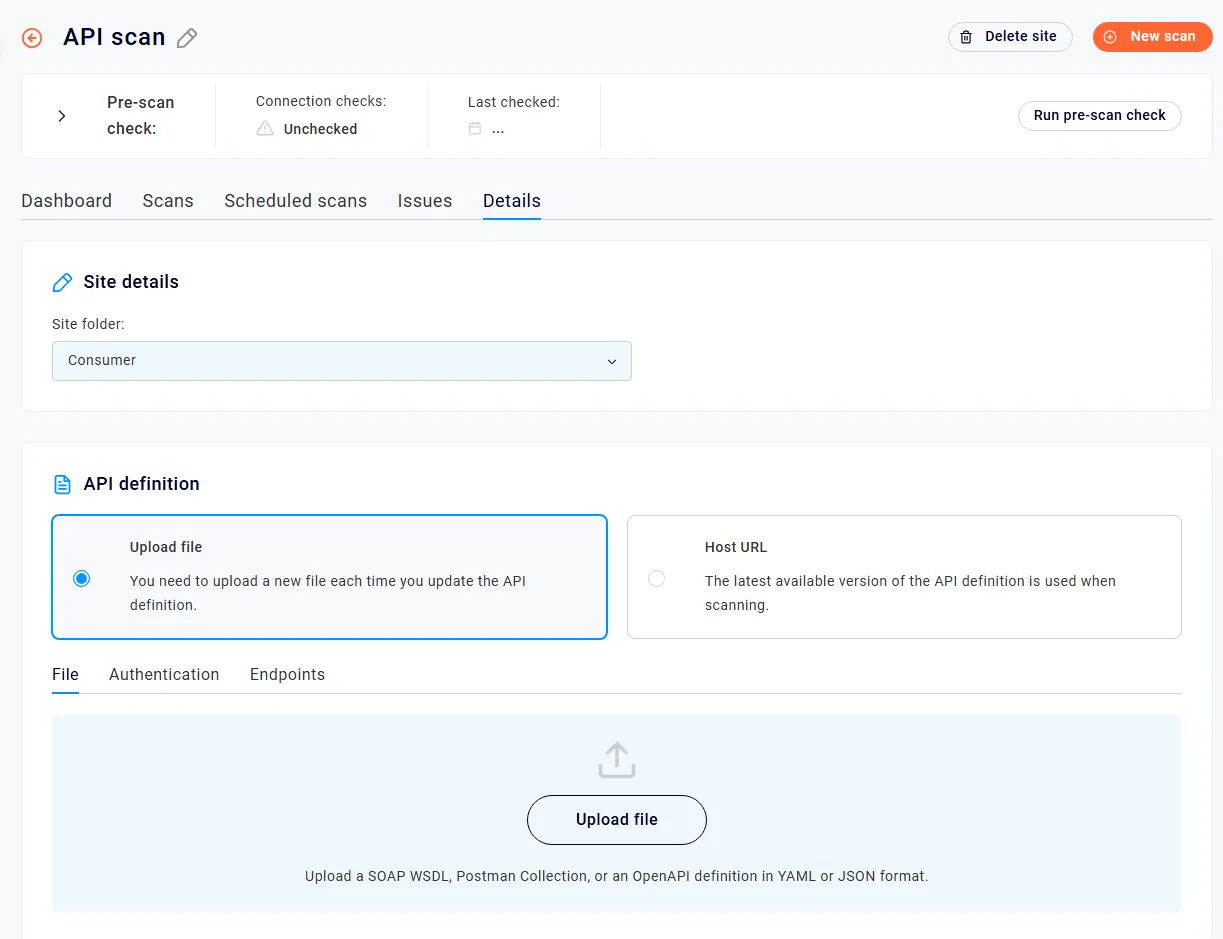
Burp Suite DAST also offers highly customizable authentication handling, making it suitable for both simple and complex authentication workflows.It supports a wide range of authentication methods, including form-based login, Basic Auth, JWT, session cookies, login recording, and more. Users can also manually configure authentication settings. For more advanced use cases, Burp also supports MFA, though it requires manual intervention or custom configurations to handle MFA effectively. However, it is not possible to verify efficiently if the authentication and scan configurations have worked well before starting the scan.
Escape: Offers straightforward scan setup for web applications and for APIs with API schema generation (learn more about it here) if users have access to Attack Surface Management product.
Once generated as, API schemas can be seamlessly integrated into the DAST process, eliminating the need for manual effort associated with uploading specifications.
Escape also emphasizes automation in the authentication setup. It supports various mechanisms, including form-based login, API tokens, JWT, or presets like Browser Automation Preset, using Playwright for browser automation actions. It is designed for simpler, less manual setups and more automated configurations.
Its proprietary AI agent automatically detects login fields, fills them in during scans, and pinpoints exactly where authentication fails, making it easier to debug and fix issues. You can test the configuration before launching the scan, as you can see on the video below:
Test scan configuration in Escape
Escape supports a wide range of authentication mechanisms, including OAuth, API keys, JWT, multi-factor authentication, Playwright-based flows, and fully custom authentication workflows.
Once authentication details are provided, Escape DAST can automatically manage sessions and tokens during the scan, reducing the need for manual intervention. This makes it particularly suited for CI/CD environments, where ease of integration and automation are key.
Depth of algorithm findings
Burp Suite DAST: Burp Suite is known for its deep and thorough vulnerability analysis, especially for web applications. It employs a combination of automated and manual testing techniques to identify a wide range of vulnerabilities. Burp Suite uses a crawling algorithm powered by their security research that can detect hidden endpoints, session handling issues, and authentication flaws. However, some of its deeper findings require manual interaction, as Burp allows users to fine-tune scans, review traffic, and inspect how specific vulnerabilities manifest. The depth of the findings is enriched by manual testing capabilities, making Burp useful for experienced penetration testers. For teams that want to ensure automation and depth of findings at scale without manual assistance, it might not be a viable solution.
I could mention is that we are kind of not super happy with the quality of the findings in Burp Suite. It's not just the false positives, but generally even if it's a true positive, usually it's relatively low-impact things that you can detect.. - Product Security Lead at Global Delivery app service
- Escape: Advanced detection algorithms identify a broader range of vulnerabilities, including complex business logic flaws like IDORs, SSRFs, and Access control issues in modern web applications. For all modern applications, Escape handles testing them natively.
- You can learn more about Escape's proprietary business logic testing algorithm here.
- And about Escape's DAST web application crawling algorithm here.
How Escape DAST enabled deeper business logic testing for Arkose Labs
Custom security tests
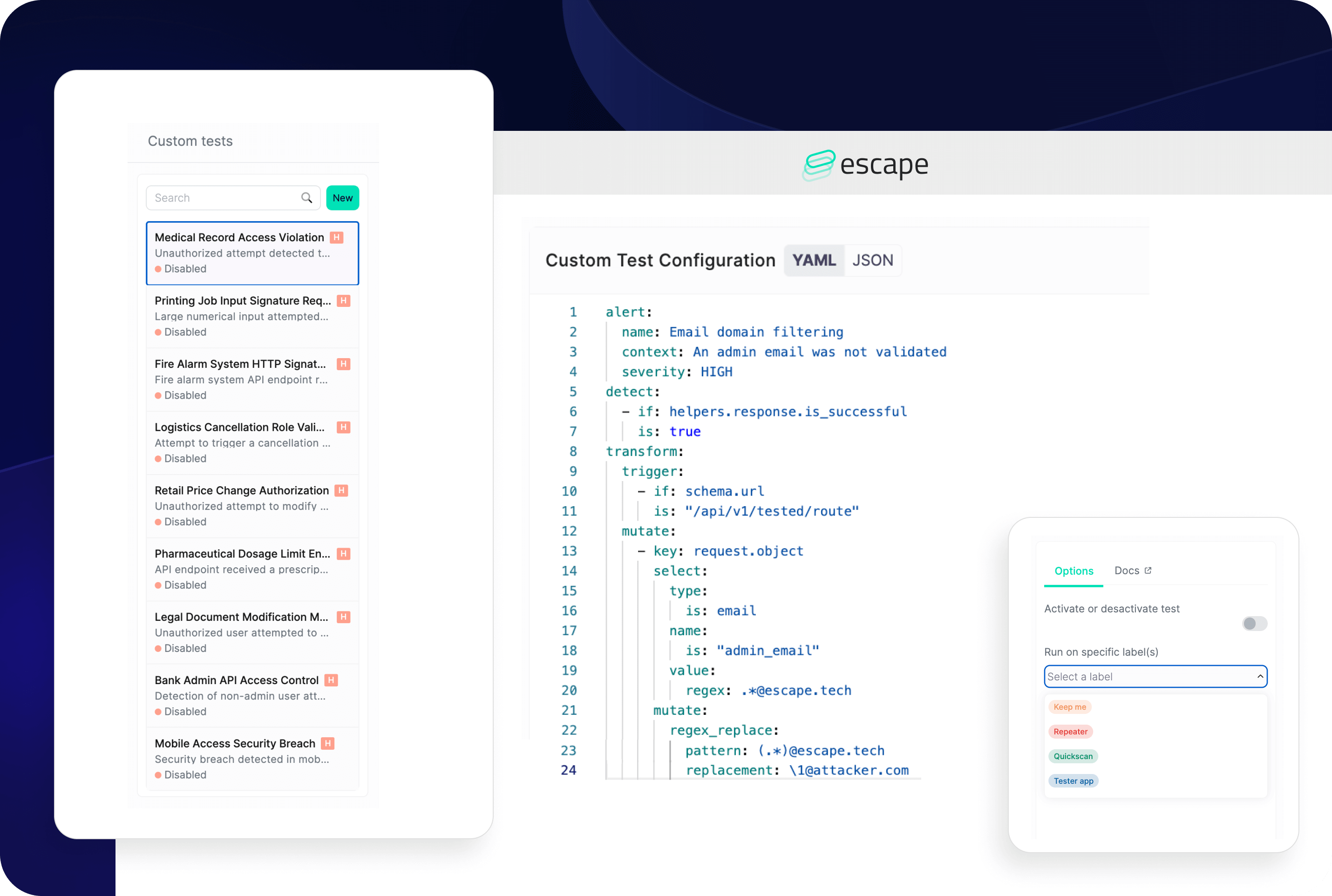
Both Escape and Burp Suite offer solutions for custom security tests. On Escape's side, this feature is called "Escape rules," while on Burp Suite's side, it's called "BChecks."
While bChecks and Escape custom tests are pretty similar on the surface, bChecks use a more verbose language, less structured like the YAML operators (detectors/transformations) that Escape uses. The biggest difference is also in the feedback-driven exploration engine and the scalar inference system that is built into Escape, helping you cover all the routes with confidence and abstractions of data manipulated and easily available through Custom Tests.
GraphQL API support
GraphQL, a query language for APIs, has gained significant traction in recent years due to its flexibility and efficiency. Escape DAST has exceptional support for GraphQL Security Testing, leveraging its membership in the GraphQL foundation and international recognition for its research in this domain.
On the other hand, according to their website, Burp Suite DAST's GraphQL crawls rely on introspection. Or you can manually interact with GraphQL APIs, for example, using Burp's extension for GraphQL (such as GraphQL Intruder or Burp Suite extensions from the BApp Store) to improve its capabilities.
Remediations
Burp Suite DAST: provides generic remediation information without offering tailored code snippets
Escape: provides remediation code snippets, tailored to each development framework, helping developers fix issues directly in the code.
Continuous testing & DevSecOps
Both tools claim CI/CD support, but the deployment realities vary.
Burp Suite DAST runs from Docker containers and integrates with Jenkins, GitHub Actions, GitLab CI, Azure DevOps, and TeamCity, but customers consistently tell us the same thing: actually getting Burp deployed in CI/CD is a project, not a setup step. We've heard from a senior AppSec engineer at a healthcare platform that authenticated testing in Burp is "pretty intensive… in terms of scalability, I don't know that there's a future for that with Burp Suite at the moment."
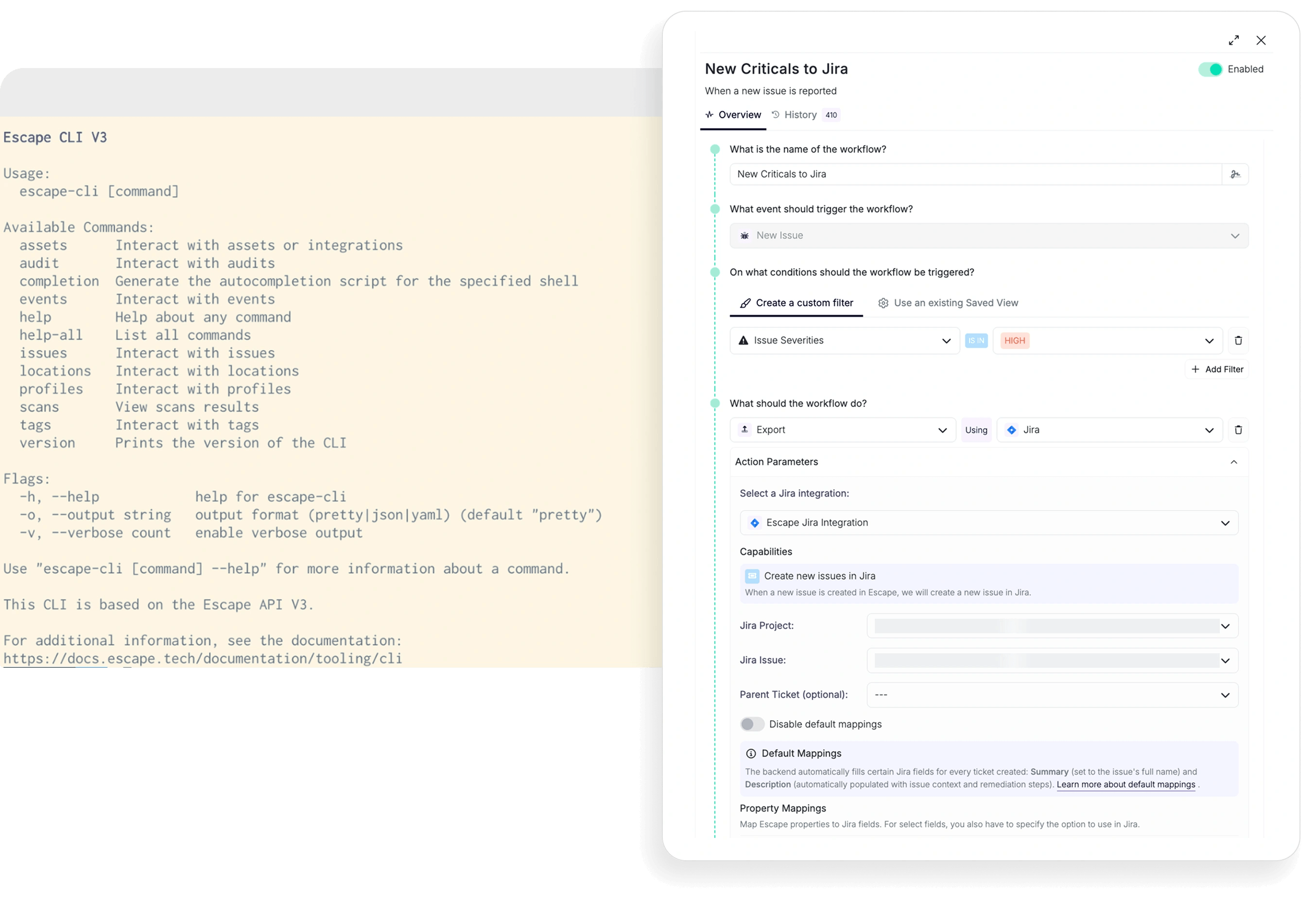
Escape was built CI-native. The Escape CLI, public API, and incremental scanning (which tests only the endpoints that changed in a PR) mean security gates live inside the developer workflow rather than alongside it. Scan profiles can be created via YAML, scans triggered via webhooks, and findings routed back to Jira, Slack, or Teams without leaving the platform.
Jira integration
Efficient collaboration and issue tracking are essential for effective vulnerability management. Both Escape and Burp Suite Enteprise provide seamless native integration with the Jira ticketing system, facilitating streamlined communication and issue resolution.
Reporting
Escape shines in this aspect with its robust reporting capabilities, offering dashboards, Compliance Matrix, customized Pentest PDF exports, CSV exports, and developer-friendly exports.
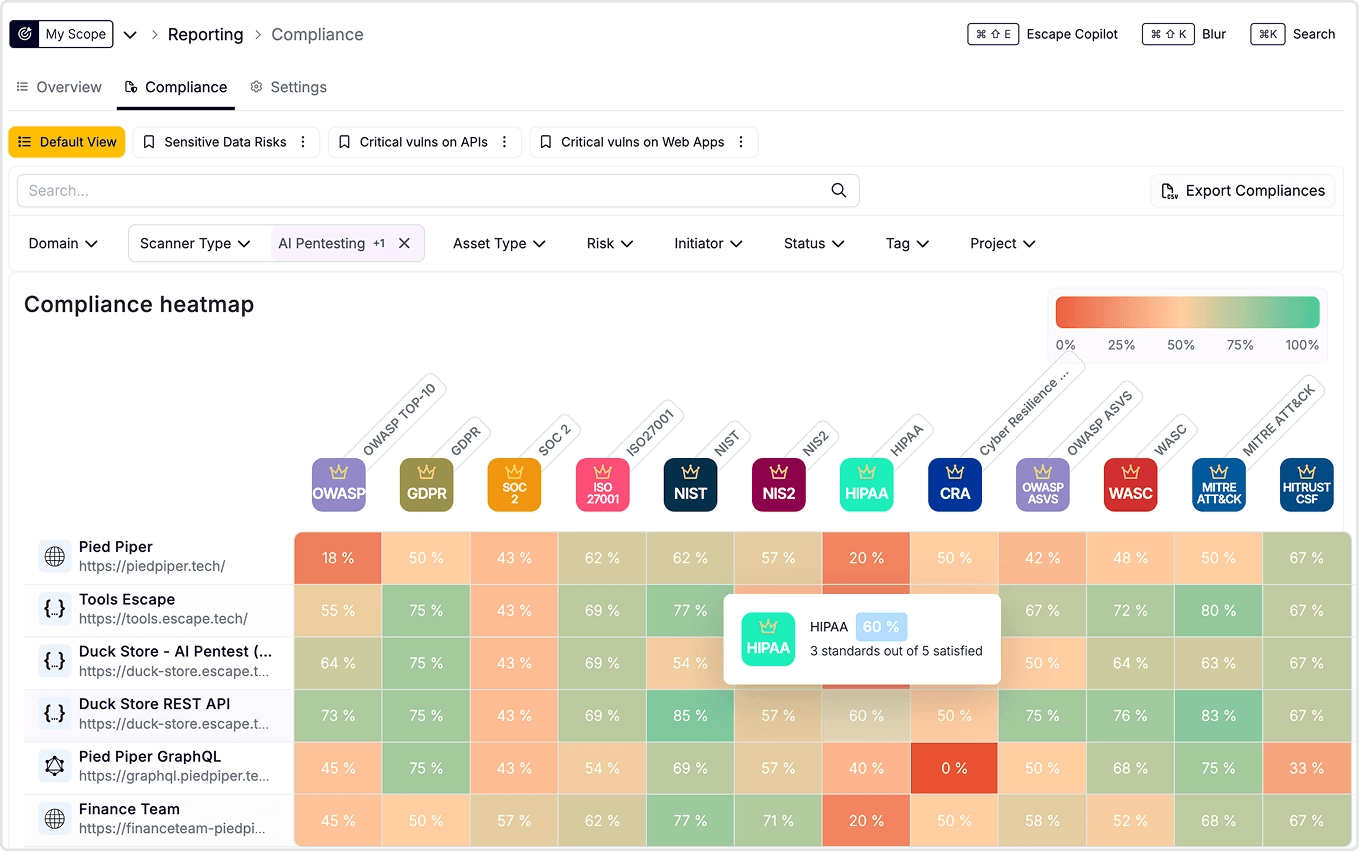
While reporting capabilities are included in Burp Suite DAST, including email reporting, aggregated issue reporting, compliance reporting, and report exporting, they are not as extensive as those offered by Escape and mainly available per dedicated scan only:
Attack Surface Management & the Wiz integration
One of the patterns we see most often in 2026 is teams realizing that finding vulnerabilities is the easy part, but knowing what to scan in the first place is harder. Burp Suite assumes you already have your inventory. Escape doesn't.
Escape's ASM discovers assets across code repositories and cloud providers, weighting them by business criticality. The Wiz integration takes this further: Escape ingests cloud assets from Wiz, runs DAST and AI pentesting against the ones that matter, and pushes findings back into Wiz's vulnerability management view. Customers describe it as a "one-two punch", surface every shadow API, then test the ones that pose real risk, all from a single platform.
Conclusion: Is Escape a viable alternative to Burp Suite DAST (formerly Burp Suite Enterprise)?
In conclusion, both Escape and Burp Suite DAST (former Burp Suite Enterprise) offer valuable DAST solutions, but Escape emerges as the superior choice for organizations looking for automated business logic security testing, especially for modern web applications and GraphQL APIs.
With its exceptional support for advanced business logic testing, proactive API discovery, seamless CI/CD integration, tailored developer remediations, and extensive reporting capabilities, Escape DAST provides a holistic approach to web application security.
FAQ
What is the best Burp Suite alternative in 2026?
For most engineering-led organizations, Escape is the strongest Burp Suite alternative. It detects business logic flaws (IDORs, access control, SSRF) that Burp misses, reduces scan times and false positives significantly, generates framework-specific code fixes for developers, and integrates natively with CI/CD. It's purpose-built for small security teams scaling coverage across many applications.
Does Escape replace Burp Suite completely?
Not for manual pentesting. If your team's primary activity is interactive pentesting and red-team assessments, Burp Suite's control and flexibility are valuable. Escape is purpose-built for automated, continuous testing—a different part of the security workflow. Many teams use both: Escape for continuous automated testing, Burp for periodic penetration testing engagements.
What about Burp AI? Doesn't that close the gap?
Burp AI is an in-flow assistant for pentesters, it helps a human probe faster. Escape's agentic architecture replaces parts of the human workflow entirely: the Multi-Agent Pentest runs reconnaissance, exploitation, and reporting end-to-end without supervision. They're solving different problems. If your bottleneck is "my pentester is too slow," Burp AI helps. If your bottleneck is "I don't have enough pentesters to cover our 200 services," you need agentic coverage.
Can Burp Suite detect business logic vulnerabilities?
Burp Suite can detect some business logic flaws (IDORs, access control issues), but it requires significant manual assistance and expert oversight. It's not systematic—finding these vulnerabilities depends on pentester skill. Escape's proprietary algorithm specifically targets business logic and detects them automatically across your entire application estate.
Is Escape better than Burp Suite for API testing?
For automated API testing at scale, yes. Escape auto-generates API schemas from code, handles GraphQL natively, and tests APIs automatically even for complex business logic vulnerabilities. Burp requires manual API spec uploads and limited GraphQL support. If you need to test a single API one time, Burp's interactive approach is fine. If you're managing 20+ APIs in active development and want continuous testing, Escape is built for that.
How does Escape handle CI/CD integration compared to Burp Suite?
Escape has native integrations with GitHub Actions, GitLab CI, and Bitbucket Pipelines. Burp integrates via REST API, requiring custom scripting. Result: Escape scans run in CI/CD in minutes; Burp requires significant engineering effort. For teams wanting to test every commit, Escape is simpler.
Can I use Escape alongside Burp Suite?
Yes. Multiple teams use both: Escape for continuous automated testing (every commit), Burp Suite for periodic penetration testing engagements (on-demand, annual). They can help to solve different problems.
Does Escape provide generic remediation guidance?
No. Escape provides framework-specific code fixes. Instead of "sanitize user input," developers get the exact code for their stack: DOMPurify for React, Pydantic for FastAPI, Spring Security for Spring Boot. This significantly reduces developer friction and MTTR.
How does Escape's business logic testing compare to Burp Suite?
Burp Suite: Limited business logic detection, requires manual pentester guidance.
Escape: Systematic business logic testing for IDORs, SSRFs, access control, multi-tenant isolation. Runs automatically without human oversight. Escape's proprietary algorithm is specifically designed for this problem.
Is Burp Suite still worth using?
Yes. But for specific use cases: manual pentesting, interactive testing, expert-led assessments. It's not the best fit for continuous automated testing, API discovery, or business logic vulnerability detection at scale.
Exploring other DAST alternatives? Check out these guides:

