Attack Surface Management, Reinvented
Your attack surface. Fully mapped to the application layer.
Legacy EASM tools find hosts and ports. Escape finds everything your engineers are actually building and exposing: APIs, SPAs, AI apps across your entire distributed org, in real-time.
Trusted by 2000+ security teams worldwide












See everything your engineers have built and exposed in under an hour.
to application layer and beyond
We map what's actually running, not just what's open.
30%
more attack surface discovered on average from Shadow APIs
Legacy EASM sees ports, hosts, certificates. Escape maps your actual application layer: every REST API, GraphQL endpoints, SPA, MCP, gRPC and SOAP your engineers are shipping. If it's exposed, we find it. Including the ones you didn't know about.
Book a demo
Book a demo
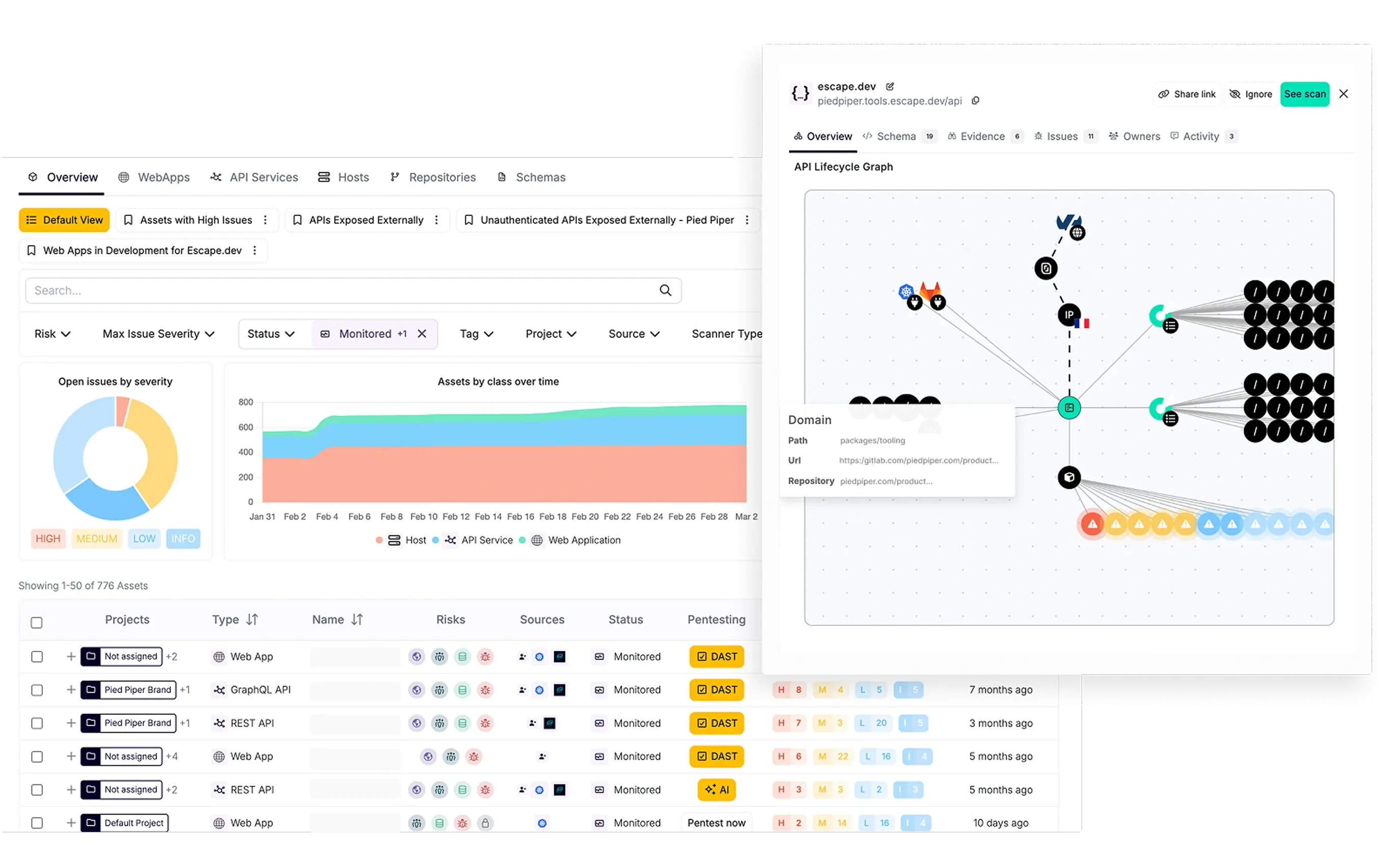
Agentless API discovery
Shadow APIs don't stay in the shadows
<1h
to map your entire api attack surface
The API shipped last sprint without a ticket. The staging endpoint that never got taken down. The MCP a developer spun up to test something.
Get instant visibility into your exposed and internal APIs, including shadow APIs, with agentless discovery scans and native connectors to your stack and route them straight into your security workflow.
Get instant visibility into your exposed and internal APIs, including shadow APIs, with agentless discovery scans and native connectors to your stack and route them straight into your security workflow.
Book a demo
Book a demo
.webp)
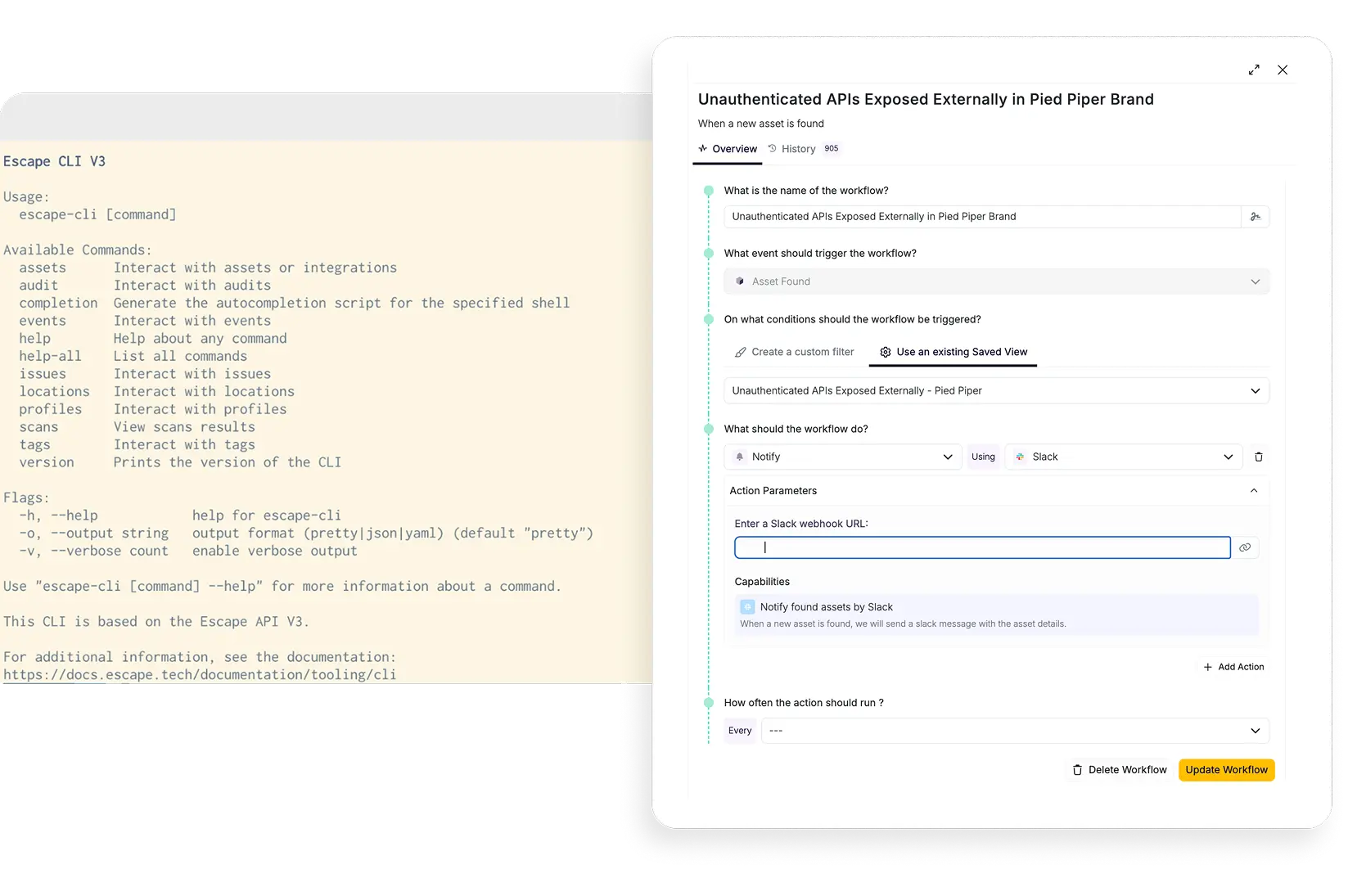
YOUR SCALE IS NOT THE LIMIT
Your org scales. Your Attack Surface Management scales with it.
12h
Saved per security Engineer per month
New acquisition, new product line, new team onboarded next quarter, sound familiar? Through powerful integrations, public API, command line tooling, and custom reporting you can automate the security onboarding and risk reduction that used to take months.
Every new asset and associated risk is discovered, attributed, scanned, prioritized and routed without anyone filing a ticket.
Every new asset and associated risk is discovered, attributed, scanned, prioritized and routed without anyone filing a ticket.
Book a demo
Book a demo
AND MUCH MORE
The details that turn asset inventory into action.
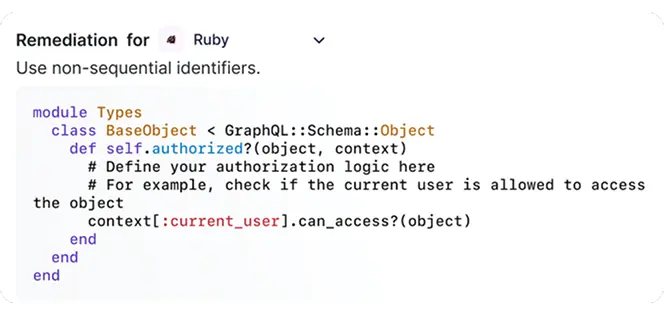
Every asset comes with a code fix and a proof-of-exploit trace - the exact request sequence that demonstrates the vulnerability is real and reachable. Your developers trust you on what was found and what they're fixing.
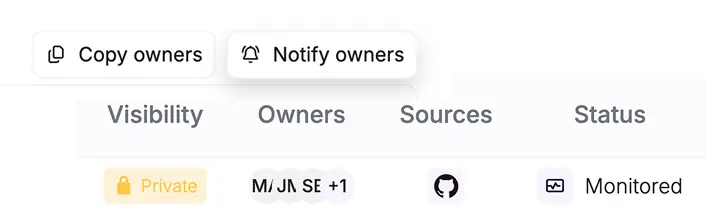
Findings reach the right engineer. Every asset is mapped to the team that built it, pulled from your repos. No more "who owns this?" Slack threads, you can route to right people directly, with full asset context already attached.

Your risk platform gets the context: Escape feeds every discovered asset into Wiz with full application-layer context: owner, type, exposure level, associated risk.
Benefits
The difference between visibility and actionable intelligence
Discover from code to cloud
Your team can now track what a distributed engineering org is actually building and expose in real-time. It's every API your engineers shipped, every SPA a product team launched, every MCP that got prototyped and forgotten.
Detect exploitable risk
There's a difference between a vulnerability that exists and one that can actually be exploited. Escape confirms it. You can now prioritize with context without second-guessing.
multiply impact at scale
Upstream, plug Escape into your integrations and code repos, and onboard new products at the same speed your org ships. Downstream, every discovered asset flows into Wiz with full application context, making your entire risk platform smarter.
Save time for engineering
With remediation-first platform, you can now respond quickly with clear ownership. Your engineers are enabled to prioritize and resolve the vulnerabilities that matter most across all products and brands simultaneously.
Don't take our word for it
What security teams say after getting full visibility.
"DoubleVerify greatly attributes a lot of their API success to the combination of Wiz and Escape simultaneously together as a unified integration. This gives us more certainty that our APIs are not only discovered but inventoried, and then tested and secured.”

“Within about an hour, we had all our API attack surface scanned and we were able to determine if there were any vulnerabilities on any of our endpoints because in stark comparison with previous vendors where it’s difficult to onboard and you don’t get good results very quickly.”

"As a global organization with a diverse digital footprint, we take advantage from Escape's platform to continuously improve the discovery and assets tracking across our entire group — including shadow IT — and to monitor our public exposure."
Shoot for the full picture
ASM that acts as the connective tissue across your environments and tools
modern frameworks
cloud environments
security tools
developer tools
Pyhton
Support makes a difference
The right security approach goes beyond time, systems, and infrastructure. It’s built on trust that lasts.
venture further
Your asset discovery is just the beginning.
Here is everything you need for continuous offensive security.
Business-logic-
aware DAST

Replace legacy DAST with business-logic-aware testing that improves over time and helps your team remediate real, exploitable vulnerabilities.
AI
Pentesting
Pentesting

Escape helps teams scale down exploitable risk, not just scale pentest output.
stop flying blind
See everything your engineers have built and exposed in under an hour.
Book a demo
Book a demo

.jpg)
.jpeg)


