AI Pentesting, Reinvented
Scale pentests within your engineering processes
Run continuous, AI-powered pentesting assessments with exploitability proof and reporting auditors and your engineers will both actually act on.
Trusted by 2000+ security teams worldwide












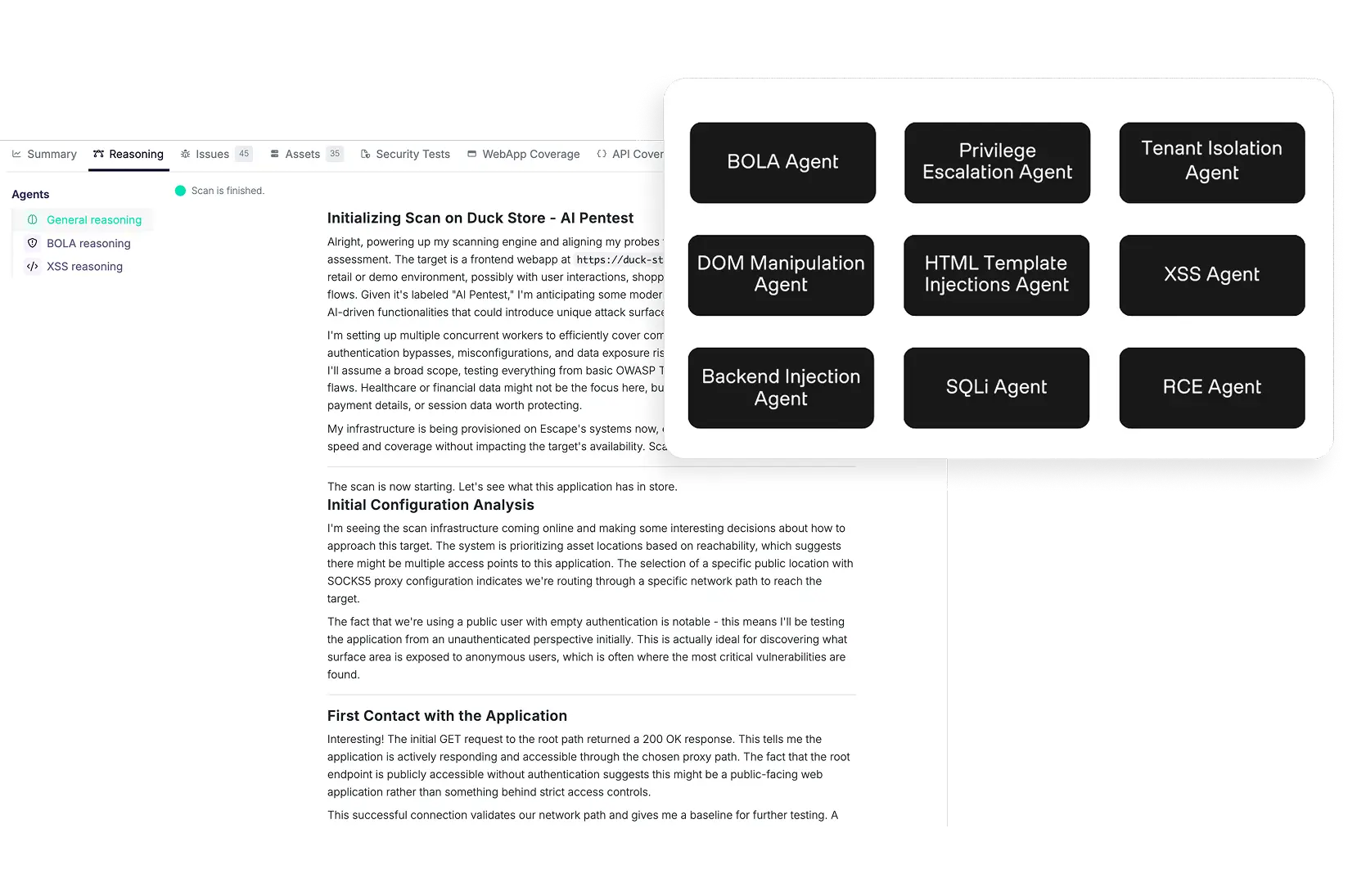
An AI that thinks like an attacker. Acts like a program.
one giant leap for automating pentesting
Human-like testing. Machine-like scale.
393%
ROI seen by security teams
Traditional pentests are point-in-time by design. Agentic attack reasoning powered by Graph context allows Escape to find even complex multi-step attack chains. You can run in-depth security assessments on every release cycle, so vulnerabilities get caught before production. Transform offensive security from a budget line into a quality gate.
Book a demo
Book a demo
vulnerabilities is NOT the final frontier
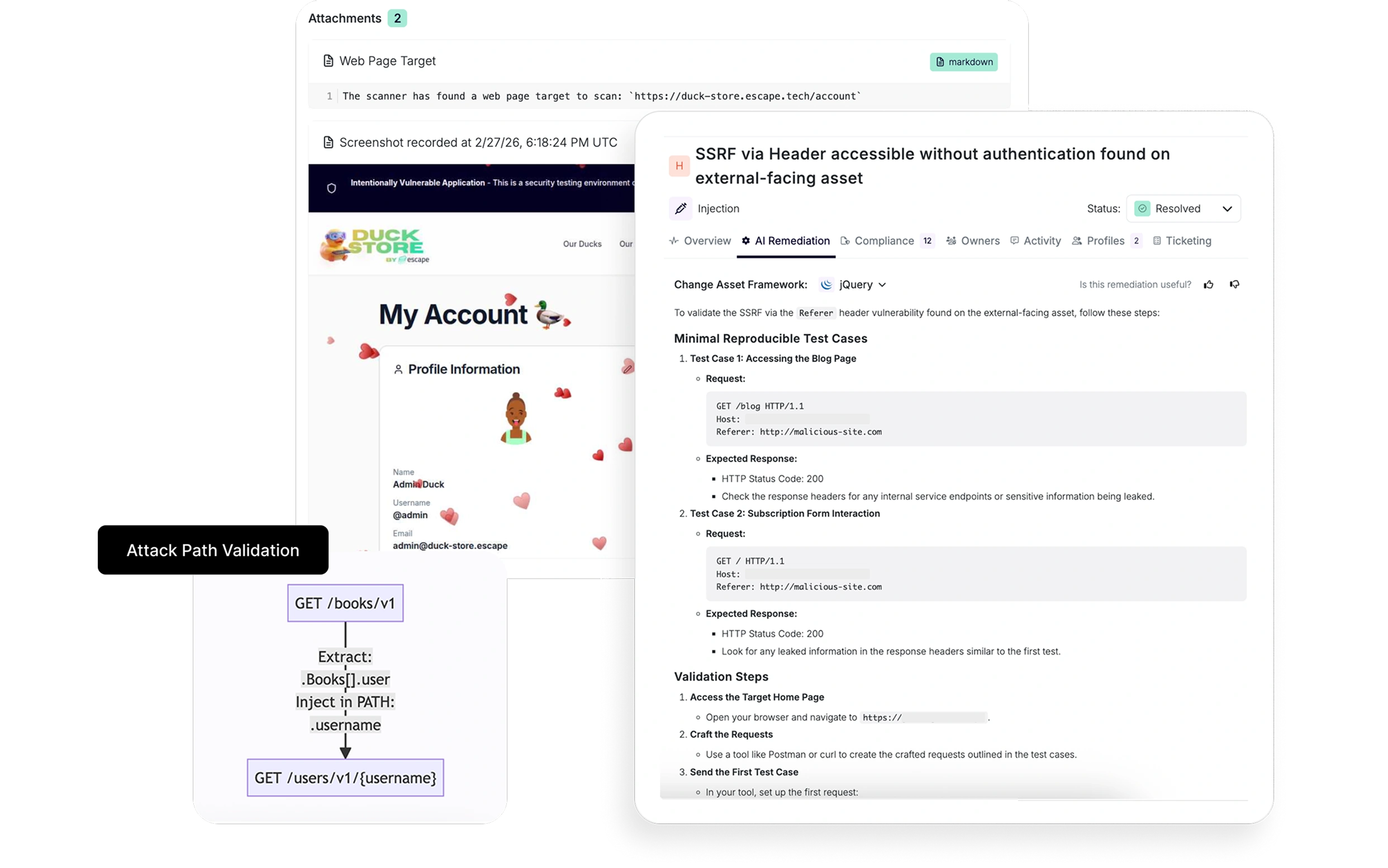
Proof that gets engineering to move
80%
time-to-remediation reduction versus manual or semi-manual processes
Engineers don't fix “we found a BOLA - use OWASP guidelines”. They fix "here's exactly how an attacker exploited this, here's the request chain, here's the fix for your framework." Escape delivers both.
Book a demo
Book a demo
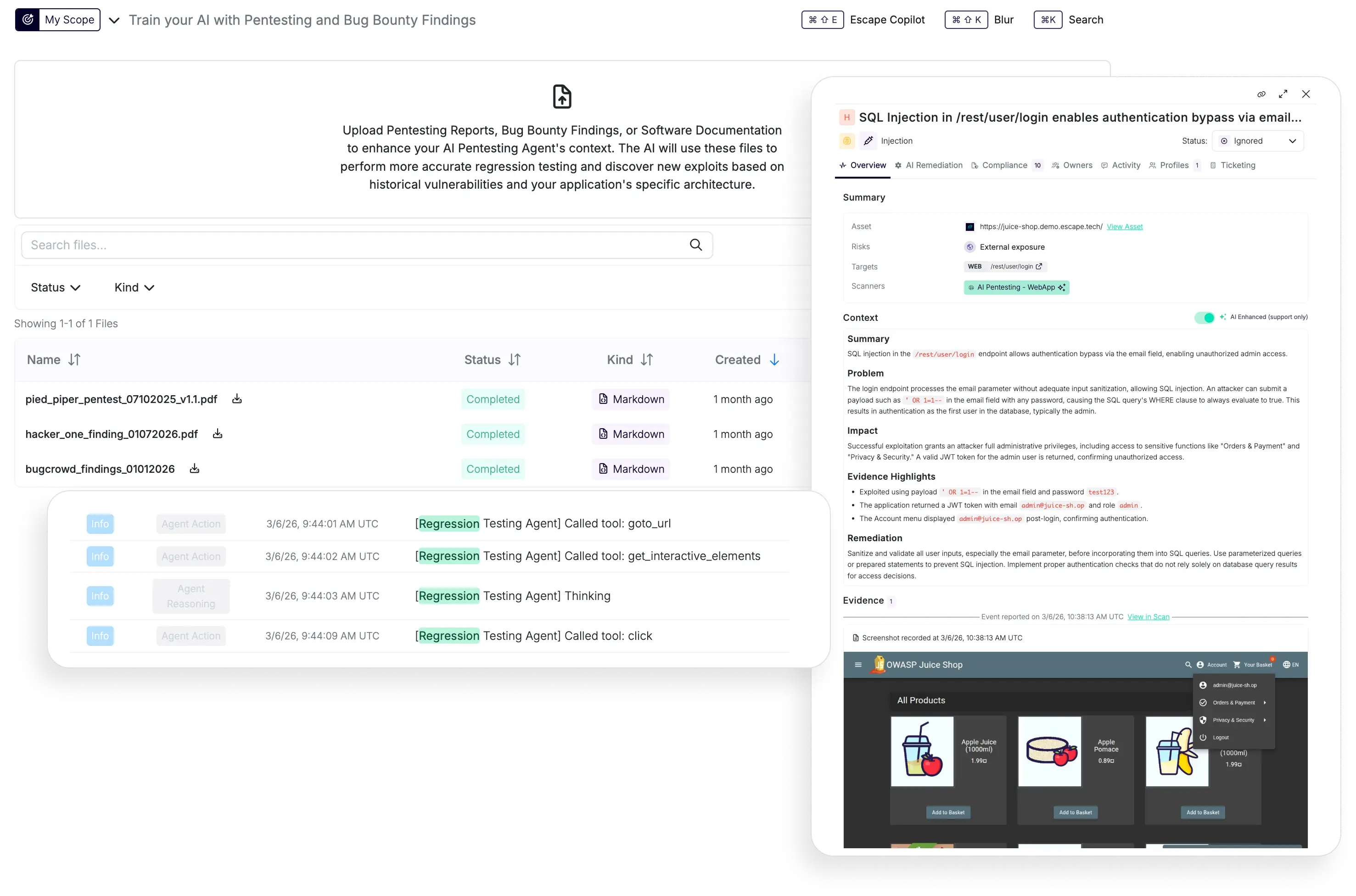
Yesterday's finding.Today's regression test.
Bug bounty to code fix,
no human needed
<1 hour
from file upload to organization-wide testing
Feed in findings from bug bounty programs or manual pentest reports. Escape converts them into automated regression tests that run on every build. The same vulnerability never ships twice, and your security posture compounds instead of resetting.
Book a demo
Book a demo
AND MUCH MORE
The details that separate a real offensive security program from a compliance checkbox.

Automations, workflows, AI-powered setup assistance. Everything is built in for a small team to scale their penetration testing program across the entire org and prove the ROI to leadership.

PCI-DSS requires application security testing on every significant change. SOC2 and ISO 27001 expect documented, regular assessments. Escape provides with detailed reporting and visibility with no human in the loop.
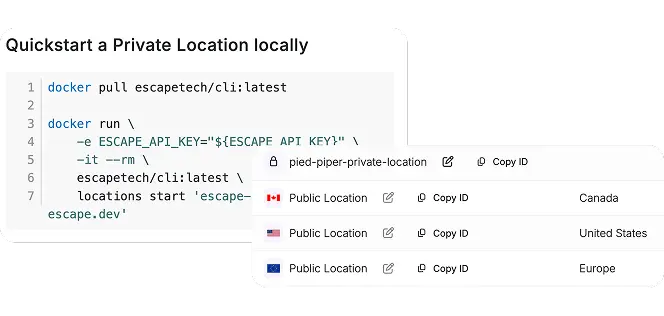
Public and private - You stay in control. Cloud and on-prem hybrid deployments mean you can run assessments even on internal applications without giving external consultants or bug hunters access to your infrastructure.
Benefits
One program. Four shifts that change how you run offensive security.
continious resilience process
Traditional pentests are siloed and point-in-time by design. Escape brings results into Wiz, routes fixes to engineers in their development environments, and runs on every release cycle.
Engineering fixes 3× faster when they see the proof
When engineers see the exact agentic reasoning trace (the graph path, the chain of steps, the working exploit), they prioritize the fix immediately instead of questioning the severity. Mean time to remediation drops.
Security gets stronger every sprint
Every vulnerability Escape finds or that a bug bounty hunter or manual pentester finds becomes a permanent regression test on every build. Your attack surface from last quarter becomes your CI gate this quarter.
PROVEN ROI
When the CFO asks what you got for this year's security spend, you show them quarterly pentests, continuous coverage, and a fraction of the traditional cost.
ready to scale your penetration testing?
Schedule a call with one of our experts
Don't take our word for it
What security teams say after automating their security testing
“It gives a good remediation process and steps to reproduce, which makes our team 10 times more efficient for validating vulnerabilities. We've been pretty lucky that the validation has been pretty solid so far, and that's a great thing to say”
.png)
393%
ROI seen by the Head of Application and Offensive Security at a large multinational organization
“Escape's IDOR scanning and multi-tenant capabilities set it apart from other security testing solutions and allow us to test multiple scenarios.”

Seamless docking. Every pentest mission.
AI pentesting that fits seamlessly into how your team already works
modern frameworks
cloud environments
security tools
developer tools
Pyhton
Support makes a difference
The right security approach goes beyond time, systems, and infrastructure. It’s built on trust that lasts.
venture further
Automating pentesting process with AI is just the beginning. Here is everything you need for continuous offensive security.
Business-logic-
aware DAST

Replace legacy DAST with business-logic-aware testing that improves over time and helps your team remediate real, exploitable vulnerabilities.
Attack Surface Management

Discover and validate exposure of modern applications, APIs, and infrastructure from code to cloud.
Don’t add headcount. add escape.
Stop scheduling pentests. Start running programs.
Book a demo
Book a demo

.jpeg)

